Around the time of Codegarden, we released a new open-source, free-to-use, Umbraco package called Authorized Services.
We've worked on releasing several integrations over the past couple of years with various third-party SaaS services. And we'll continue to do so. If they match a service you also need to work with for a particular use case, they'll save you quite a bit of development time. Even if they don't match exactly, being open-source they'll be a useful starting point for anyone considering similar integrations with Umbraco.
There's a limit to the value we can provide here though. The number of available SaaS providers is enormous these days, so it's unlikely we'll be able to work on even a fraction of these. Plus of course, there are many services that can be integrated into an Umbraco solution, even if there's not a common use case for why you'd need an integration in the backoffice.
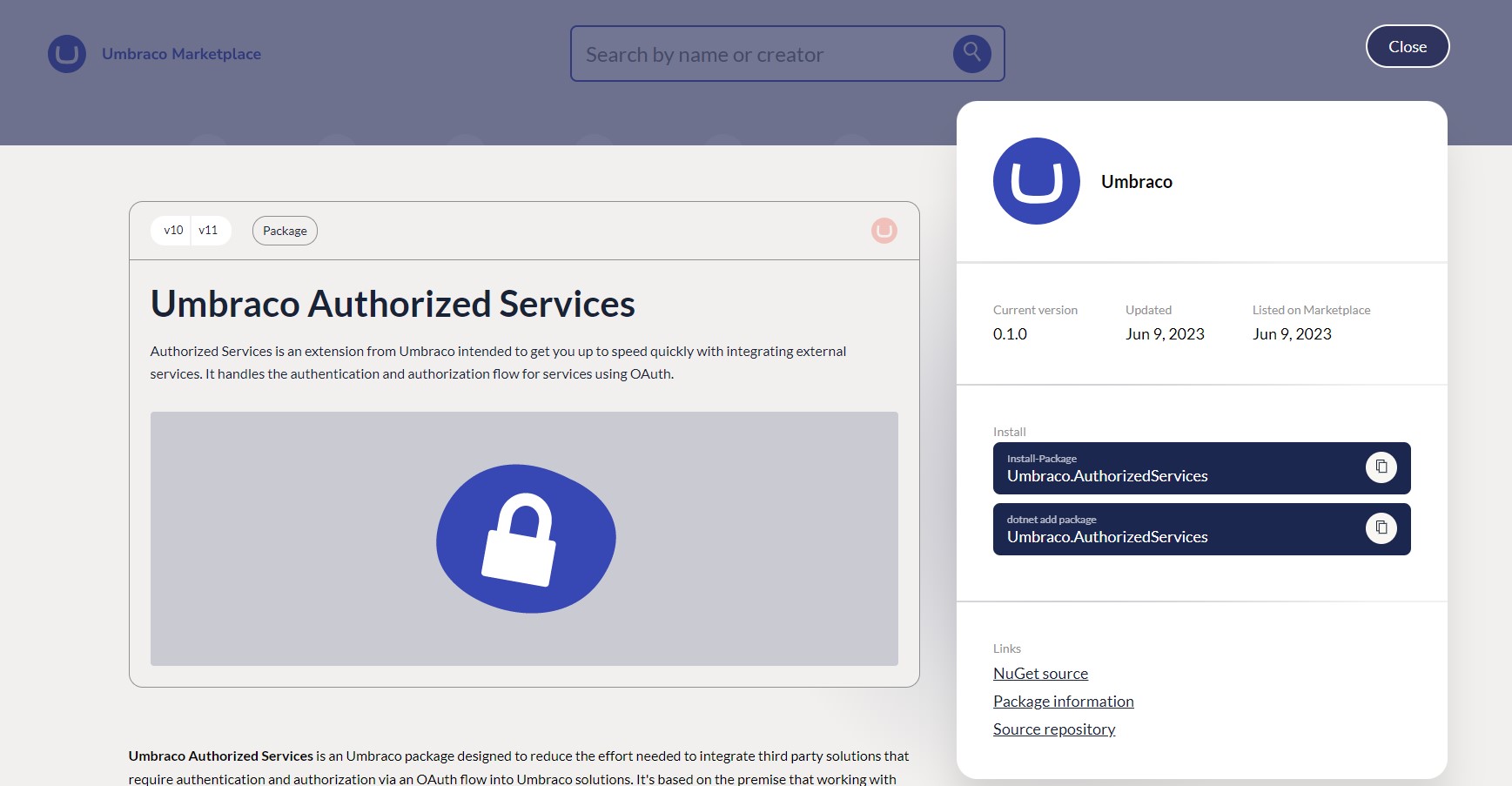
As such we decided to focus also on building the Authorized Services package. The idea is that we provide various aspects of the "plumbing" necessary for integration with third-party services - such as authorization, token storage, and serialization - leaving you able to focus on implementing the specific business features you need using the service's API.
If this package is new to you, it's worth first reading the blog post where we introduced it.
We also have a page on the Umbraco documentation website, where you can find full details of all configuration options - including all the new ones discussed in this article.
Otherwise, please read on to hear about how we've extended the functionality over the past few months.