
Umbraco CMS Security Advisory, March 10, 2026
Security Patches for Umbraco 16 and 17 are now available

Who’s affected?
Versions affected:
Umbraco 16.0.0 - 16.5.0
Umbraco 17.0.0 - 17.2.1
Unsupported versions can be subject to the vulnerability, but will not receive a patch. We recommend upgrading to a supported major version.
How to fix the vulnerability
A patch is available for the latest minor versions of Umbraco 16 and 17. As we are looking at a patch upgrade, and the fix is straightforward, we expect the update to only require minimal effort per project.
Instructions on patch availability and how to upgrade can be found in the release notes for Umbraco 16.5.1 and Umbraco 17.2.1.
Automatic fix on Umbraco Cloud
All Umbraco Cloud sites running the latest minor version of a supported version are patched via the automated patch feature. The security patches will be rolled out to Umbraco Cloud today to ensure all sites have been fixed.
If a project is not running the latest minor version (16.5.x, 17.2.x), the patch can be applied using the minor upgrade feature.
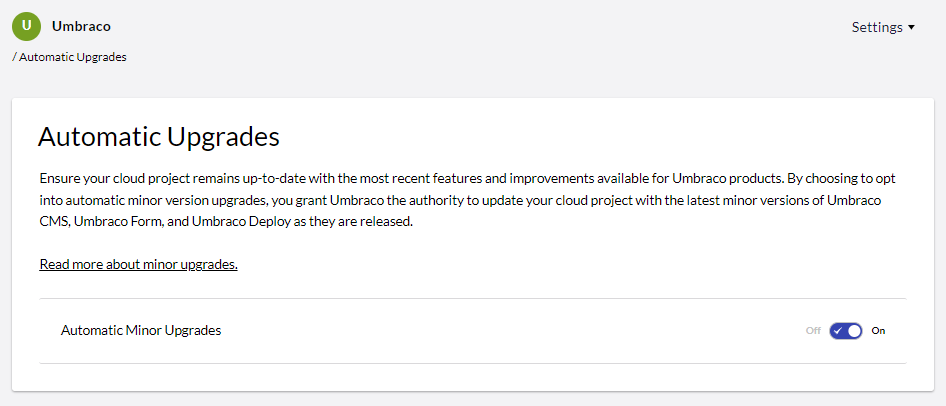
ℹ️ Note that Umbraco Cloud also supports automated minor upgrades. This can be enabled on a per-project level and ensures you're always ready to receive the latest patch.
What we know about the vulnerabilities
1. Vertical Privilege Escalation via Missing Authorization Checks
An insufficiently authorized endpoint in the management API allows a user to elevate the privileges of themselves or another user by assigning them to additional user groups.
We have evaluated this as a high vulnerability, though it is significantly mitigated in practice by the fact that the user's account must already have access to the "Users" section, giving them permission to update user details. In most Umbraco setups, such users are already part of the "Administrators" group (and, until relatively recently, had to be).
You can read more in the published security advisory.
2. XSS Vulnerability With Property Descriptions
An authenticated backoffice user with access to manage content types can inject malicious HTML via Umbraco backoffice tags into property type descriptions. Due to an overly permissive attribute check, event handler attributes such as onclick and onload were not filtered.
We evaluate this as moderate and again note the mitigation that the attack can only be carried out by a user already been given or having obtained access to an account with permission to the "Settings" section.
You can read more in the published security advisory.
3. Backoffice API Allows Unauthorized Modification of Domain Data
A backoffice API endpoint allows authenticated users to assign domain-related data to content nodes without proper authorization checks.
The issue is caused by insufficient authorization enforcement on the affected API endpoint, whereby via an API call, domains can be set on content nodes that the editor does not have permission to access (either via user group privileges or start nodes).
You can read more in the published security advisory.
Credit
We'd like to thank Sho Odagiri at GMO Cybersecurity by Ierae, Inc. for reporting the issues and responsible disclosure of details regarding the vulnerability.
Any questions?
If you have any questions or comments about this advisory, make sure to get in touch with us directly on the Security Advisories. Alternatively, you can reach out to the dedicated security email address listed at https://umbraco.com/security. Here you can also find information on how we handle security-related issues.
For direct communication related to security in Umbraco products, please sign up for the dedicated security mailing list.